Ignimission Identity connects and orchestrates across your entire identity stack, from SailPoint and Okta to CyberArk and ServiceNow. Continuous discovery, risk scoring, closed-loop remediation and governance evidence, all in one place.
Your identity stack, connected. Your posture, controlled.
Identity is your largest attack surface and the hardest to govern. Accounts multiply, roles accumulate, orphan accounts go undetected, and audits still rely on manual evidence collection. Ignimission Identity is an automation and orchestration platform that connects your IAM, IGA and PAM stack. It automates lifecycle events, scores risk continuously and generates audit-ready evidence, without replacing your existing tools.
Ignimission Identity sits above your existing stack. It connects to every IAM, IGA and PAM provider you already run, without replacing a single tool or launching a transformation project.
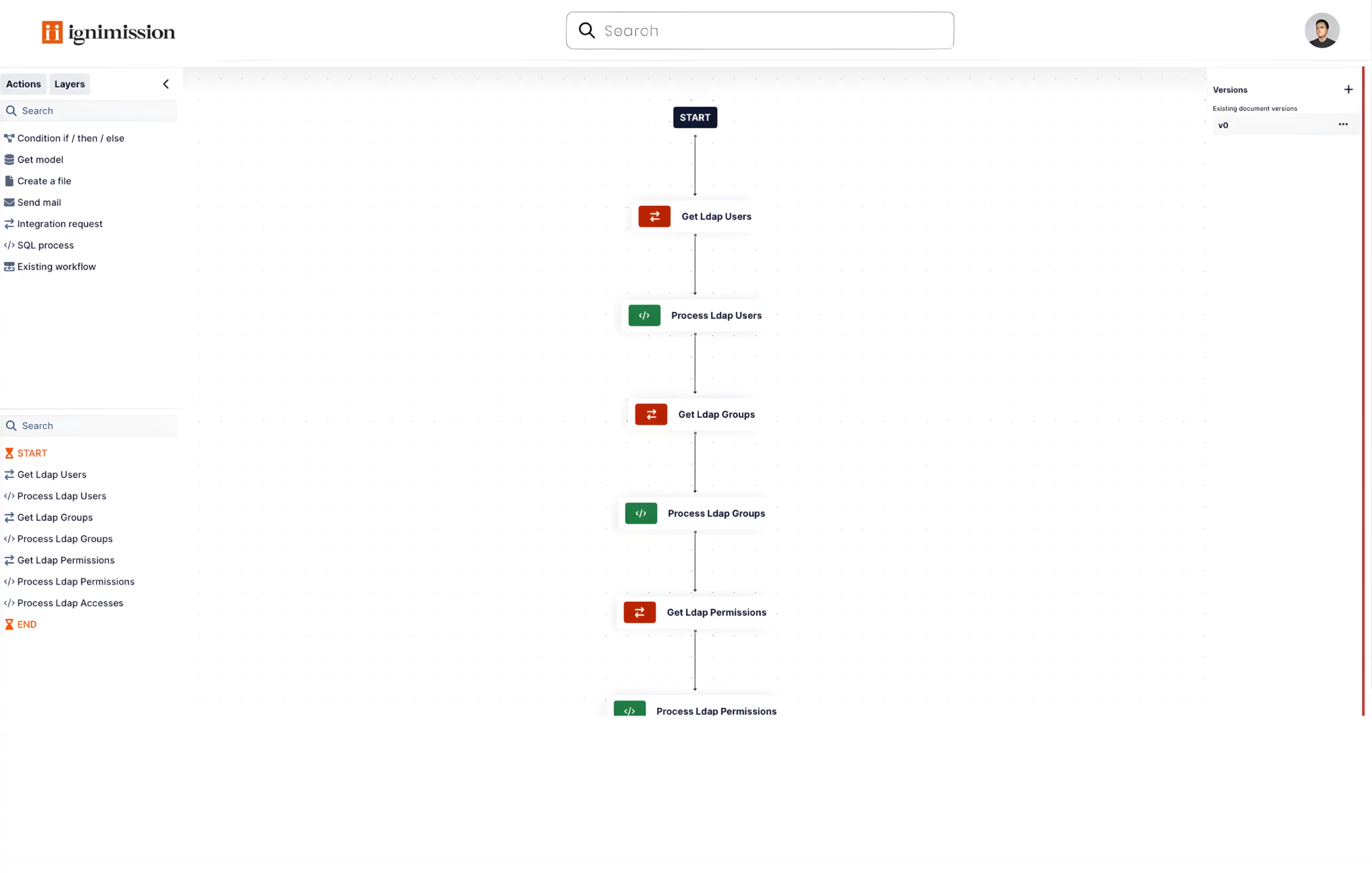
Configure identity workflows, detection rules and remediation flows in natural language. The AI-powered flow builder accelerates setup from days to hours, and adapts to your environment without developer resources.
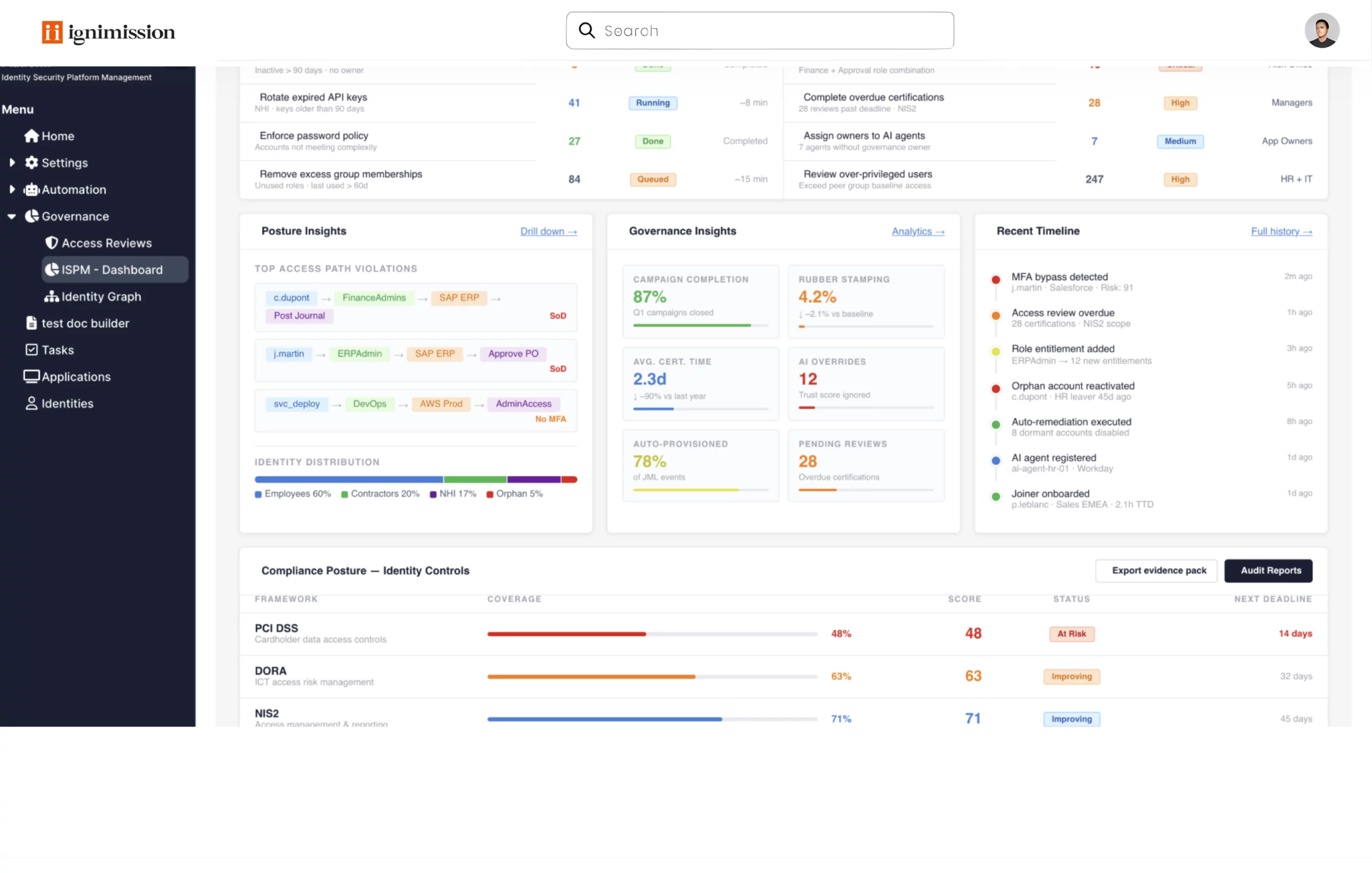
Evidence is generated continuously, not assembled before each audit. Every decision is logged and every action is traced. When an auditor asks, you answer in one click.
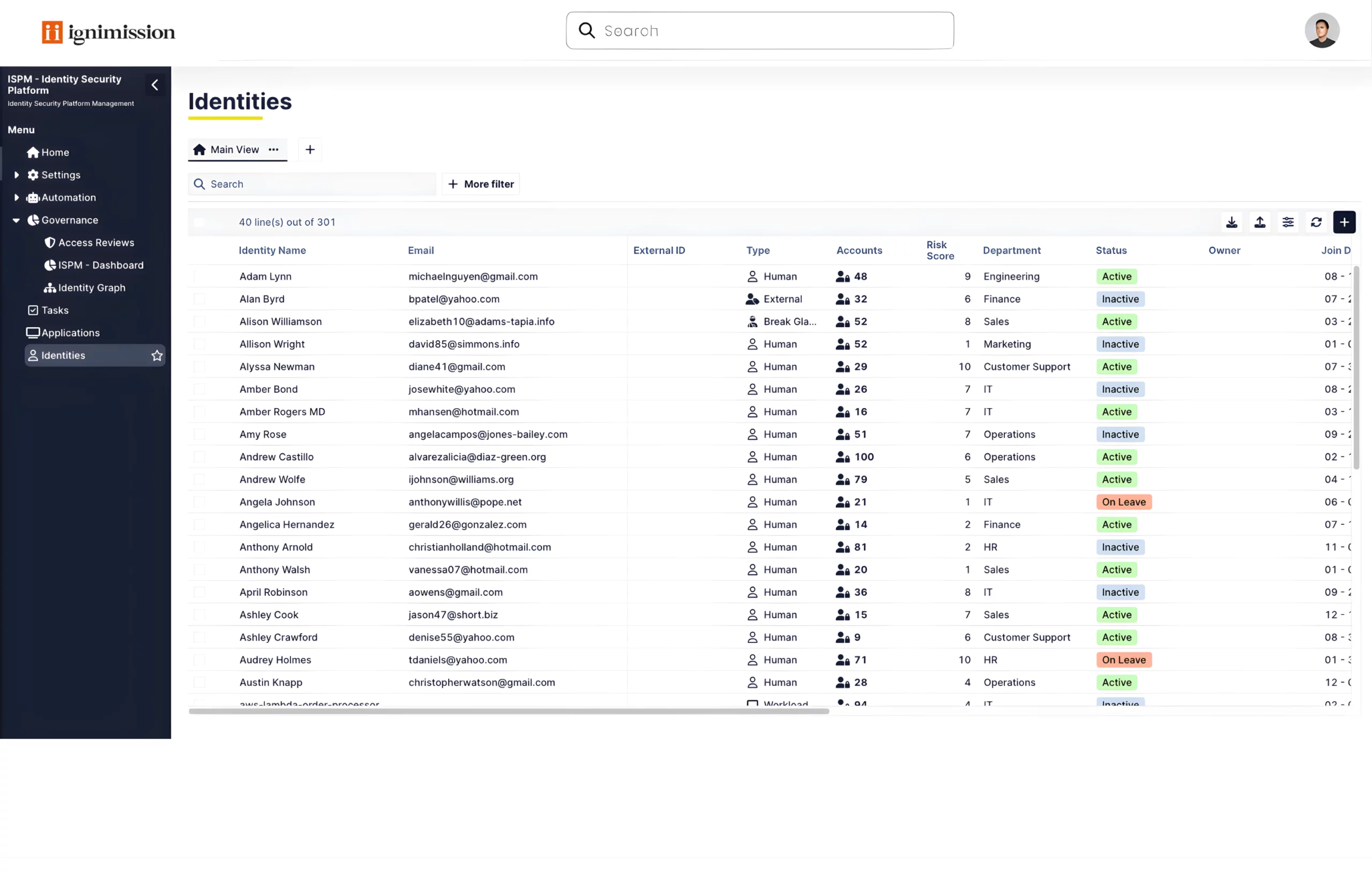
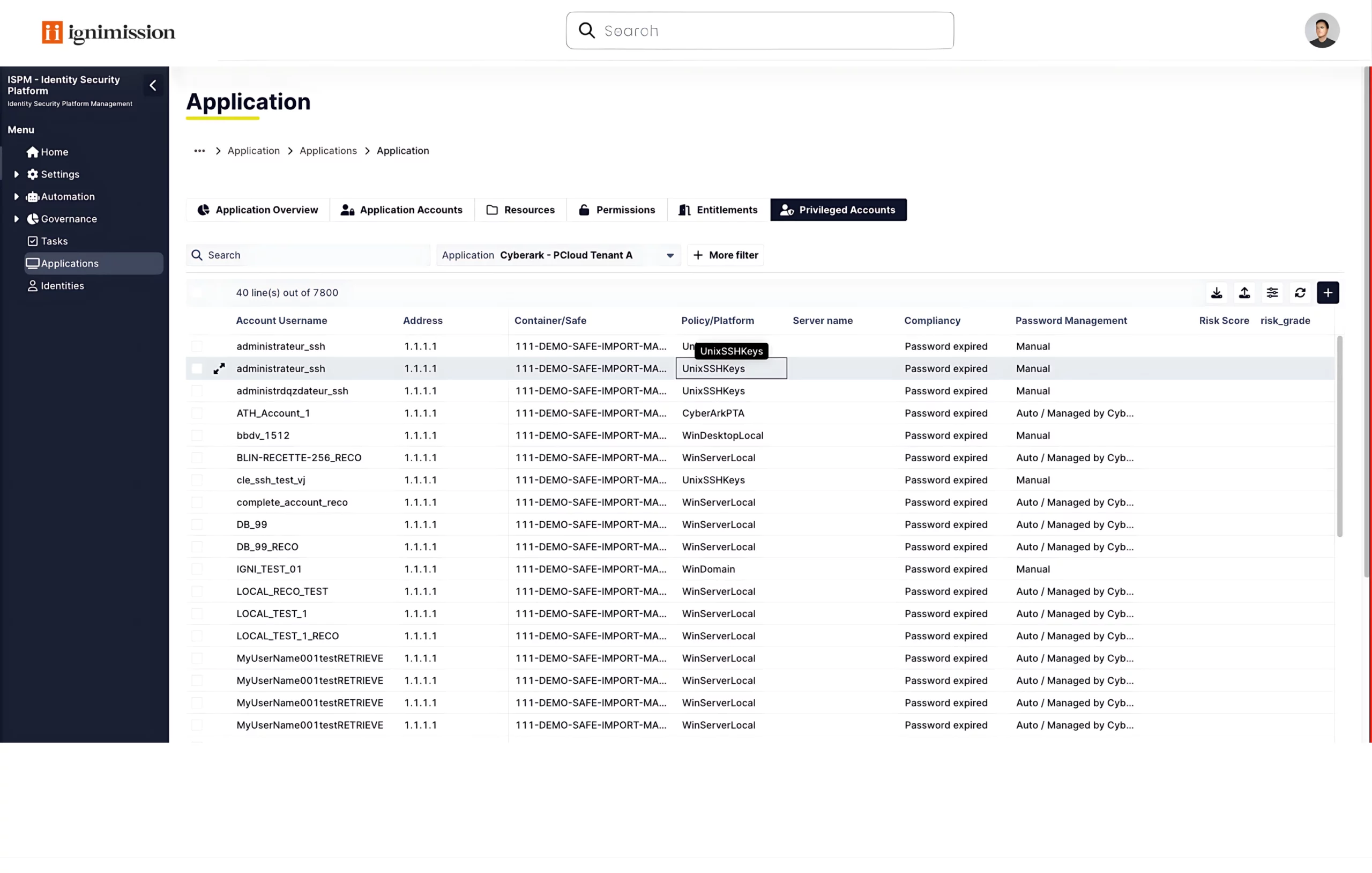
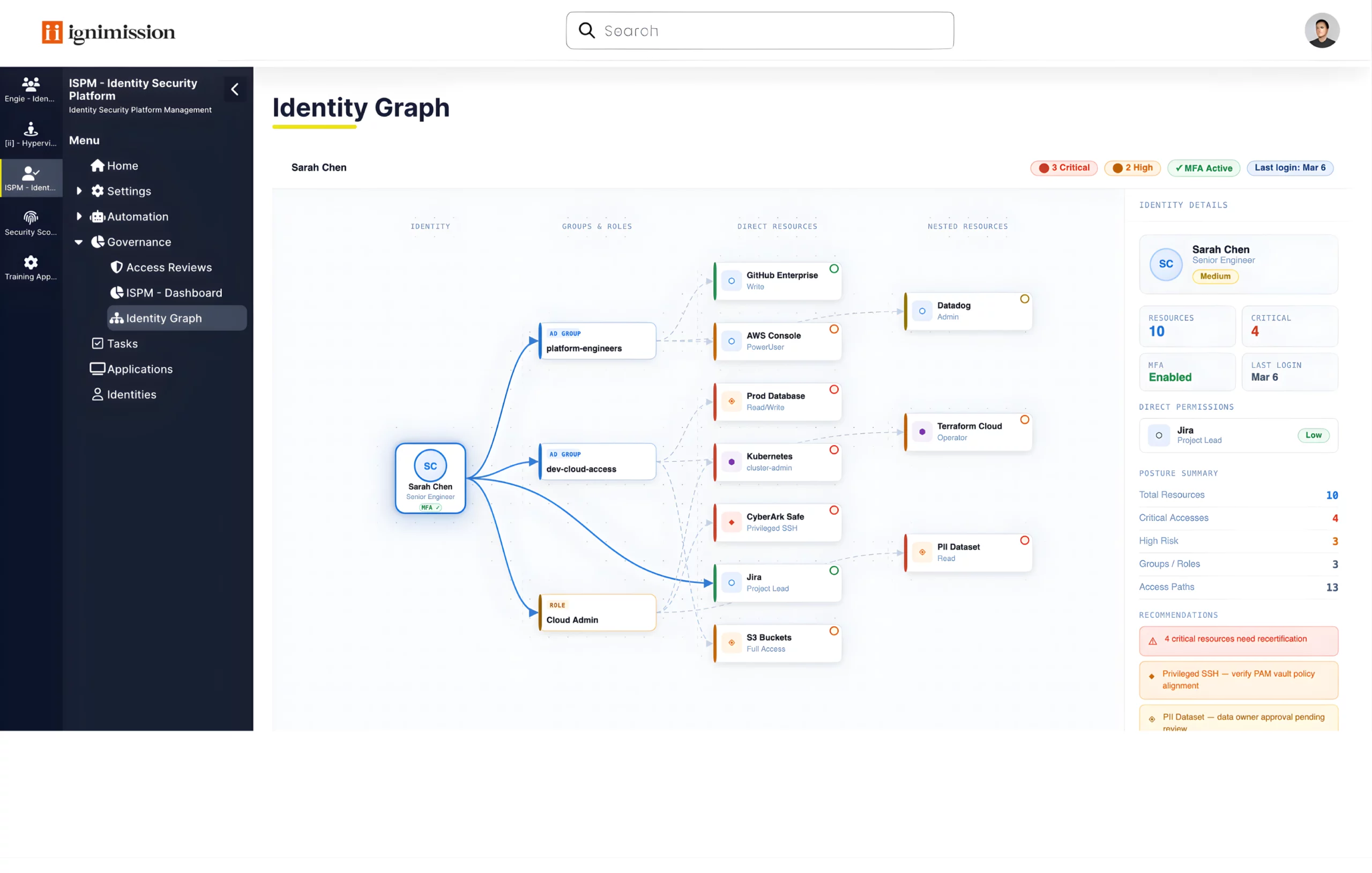
A complete, unified view of all identities, internal, external and technical, across every connected system. Built automatically from your live connectors, it answers the question every CISO needs to answer: who has access to what, and should they? LDAP, SaaS and on-prem account discovery, privileged vs. non-privileged classification, graph view of access, sensitive access labelling, orphan and dormant account detection, and cross-system account correlation.
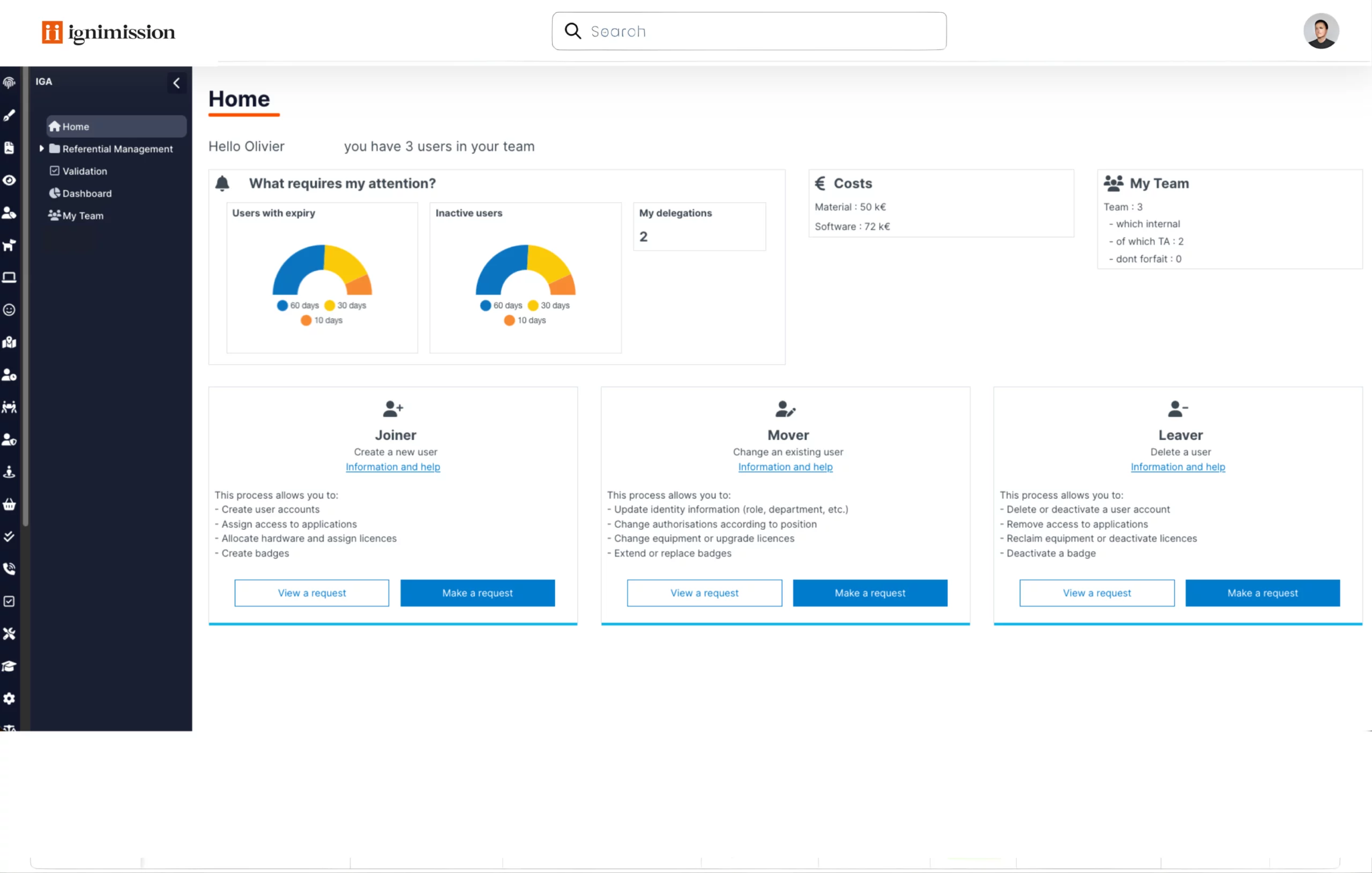
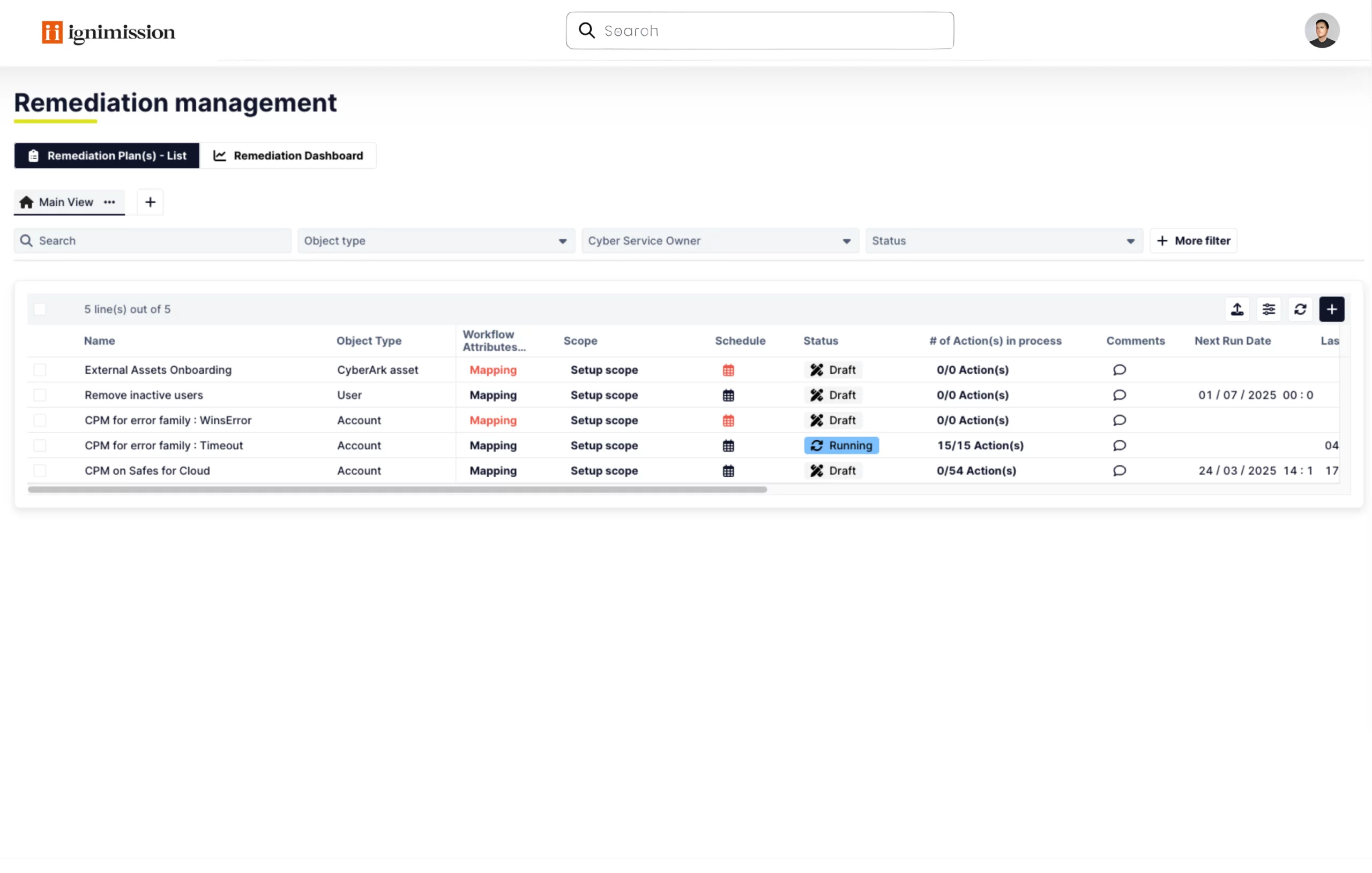
Automate the full Joiner-Mover-Leaver cycle with deprovisioning verification and exception handling. Every lifecycle event, including new hire, role change, departure and contract renewal, triggers the right actions automatically across every connected system, without manual steps. Automated onboarding and offboarding flows, role-change provisioning (RBAC/ABAC), end-date handling, verified deprovisioning, temporary access with expiry, and break-glass processes with full audit logging.
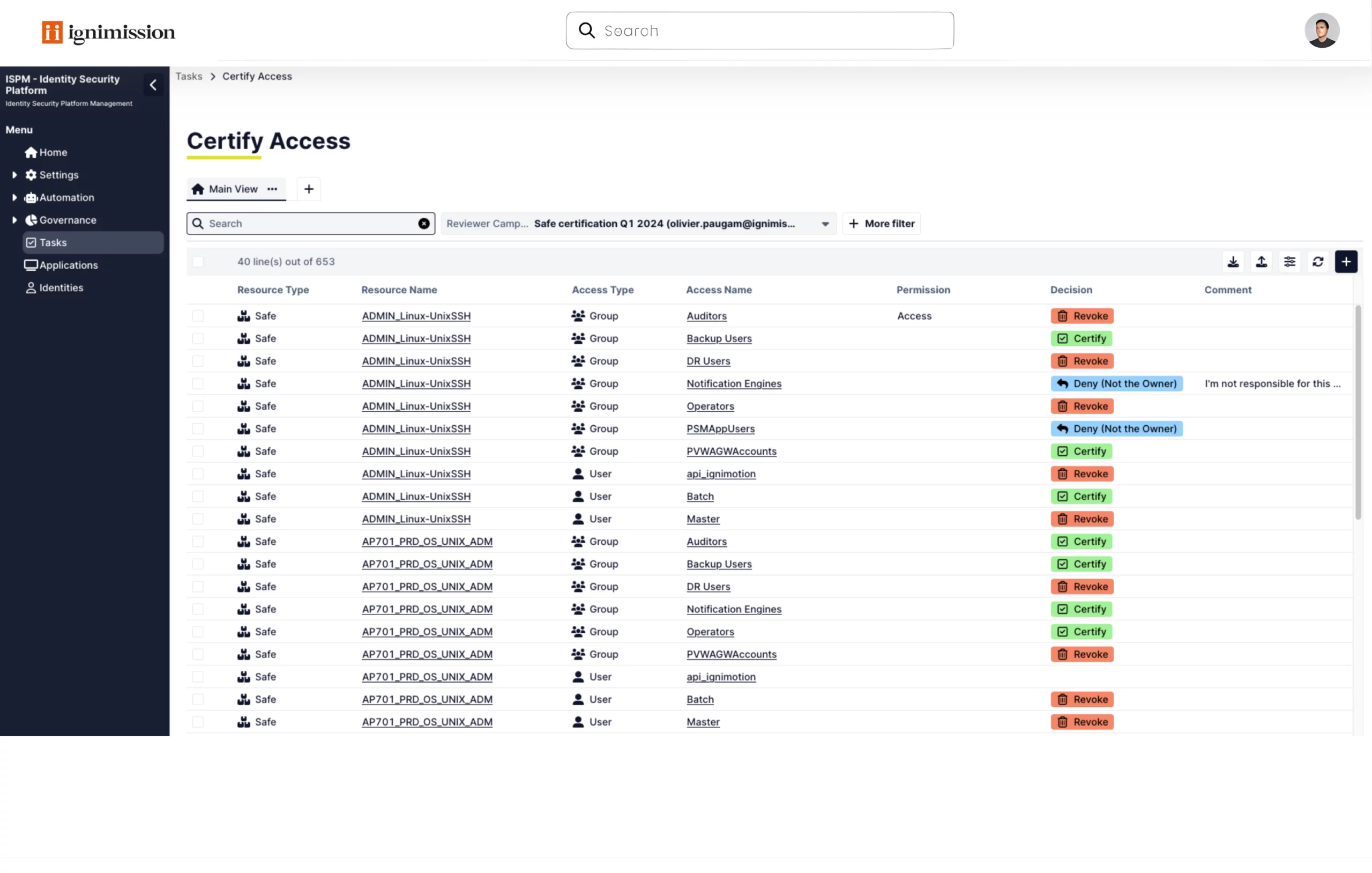
Risk-based recertification campaigns with full decision capture and evidence trail for auditors. Reviewer notifications, escalation paths and the owner access review portal are fully automated, so campaigns that used to take months now close in days. Campaign cadence and SLA control, privileged and SoD-scoped reviews, decision capture with full traceability, automated notifications and escalation, and exportable audit evidence packs.
Continuous ISPM monitoring with risk scoring, KRI dashboards and trend tracking over time. Every identity is scored dynamically based on privilege level, dormancy, SoD conflicts and drift from baseline, so your team always knows where to act first. Dynamic scoring, over-privileged user detection, orphan and dormant account alerts, permission sprawl detection, executive dashboards and long-term risk trend tracking.
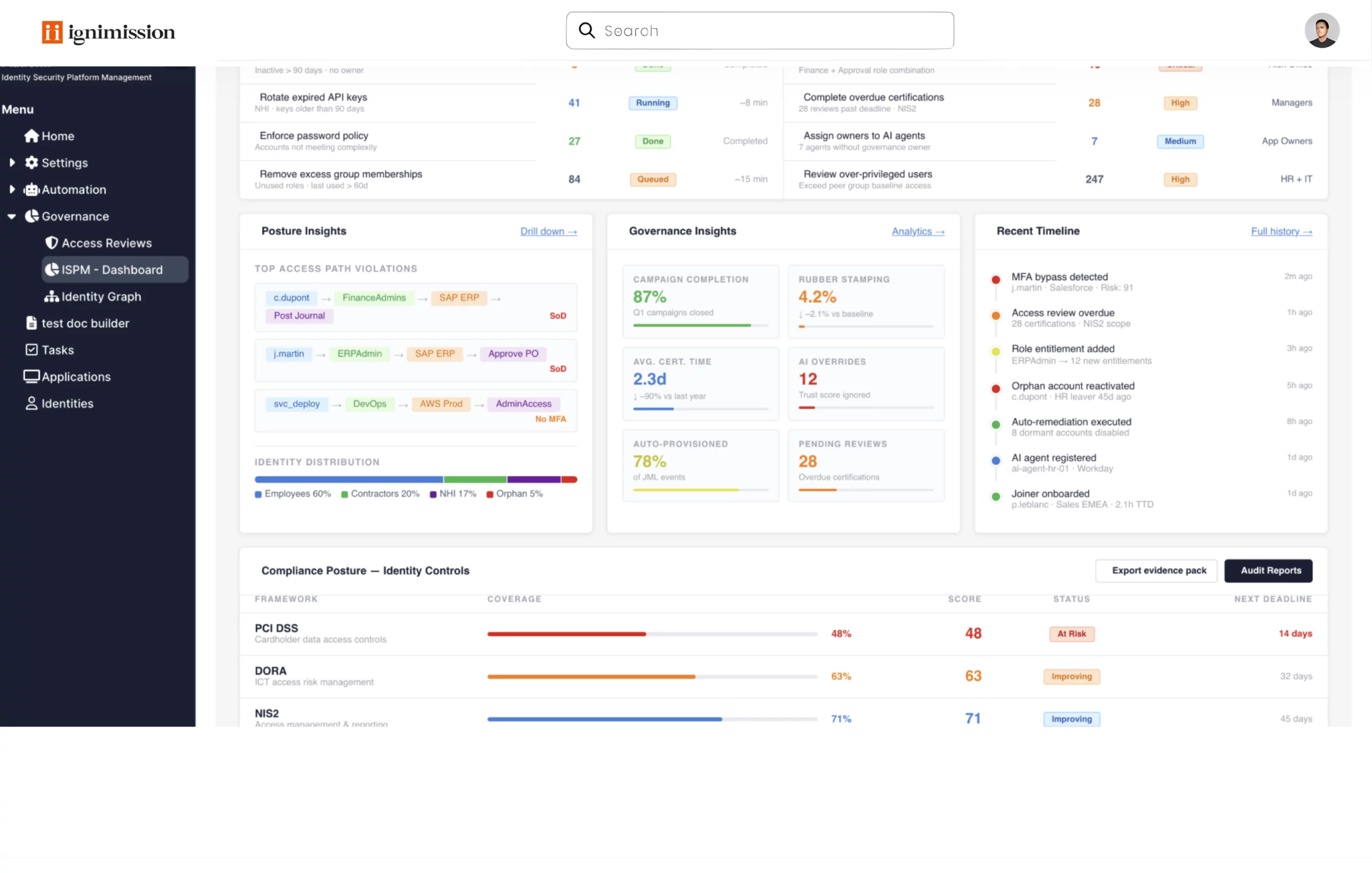
No-code automation workflows that detect, act, verify and log, with approval gates for privileged actions. The full cycle runs without manual intervention. Low-risk issues are auto-fixed, while sensitive actions require documented approval before execution. Detect-to-ticket-to-execute-to-verify loop, bulk campaigns on unused access, approval-aware workflows, event-triggered playbooks, and remediation plans with owner assignment and tracking.
Bridge your IGA and PAM layers with a unified governance model across CyberArk, Wallix, BeyondTrust and other PAM providers. Track privileged account ownership, run recertification campaigns across your full privileged population, and maintain KRI dashboards for your entire privileged estate, regardless of underlying PAM platforms. Multi-vendor governance, IGA and PAM policy alignment, SoD detection and native extension for Protec for CyberArk users.
Always audit-ready. Generate exportable evidence packs and compliance reports on demand, covering every identity action from request to remediation. Exportable evidence packs including requests, approvals, provisioning actions, review decisions and remediation logs, compliance-friendly reports by control theme such as least privilege, SoD, leavers and privileged access, full audit trail from request to approval to provisioning to removal, and readiness for ISO 27001, SOC2, NIS2, DORA and SOX.
Build automated identity workflows without writing a line of code. Connect HR systems, AD, IGA and PAM platforms into end-to-end processes, from onboarding to decommissioning, with multi-level approval gates and full audit logging. No-code workflow and campaign builder, Joiner-Mover-Leaver automation, multi-step approval chains, and scheduled or event-triggered execution.
Deploy IGA at scale with unlimited users and projects.
Choose cloud or on-premise deployment based on your infrastructure and constraints.
Connect HR, IAM, ITSM and business applications via REST APIs and configure workflows in no-code.
Talk to an Ignimission identity expert and see the platform in action on your environment.

We will be attending the InCyber Forum Europe 2026 in Lille. An opportunity to show you how Ignimission Platform helps cybersecurity teams regain control over their security framework. Each year, this event brings together decision-makers, experts, and software vendors to address key challenges in information systems security, risk management, and regulatory compliance. Increasingly complex IT […]

Ignimission Protec: Unify and Orchestrate Your CyberArk Estate at Scale As enterprises expand their Privileged Access Management programs, complexity grows rapidly. Multiple tenants, hybrid cloud and on-prem infrastructures, expanding privileged account scope, and increasing audit pressure create operational strain on PAM teams. While CyberArk is the industry benchmark for Privileged Access Management, large organizations now […]

IT & Cybersecurity Meetings 2026: Driving Cyber Governance, Automation, and Security Management Ignimission and Inetum will jointly participate in IT & Cybersecurity Meetings 2026, taking place on March 18–19 in Cannes. The event brings together IT and cybersecurity decision-makers from large enterprises through qualified one-to-one meetings and experience sharing focused on operational challenges. CISOs, RSSIs, […]
How can access recertifications be automated while maintaining audit-ready traceability?
Automated recertification relies on structured campaigns targeting high-risk access (privileged rights, sensitive access, inactive accounts or SoD conflicts).
Ignimission enables precise scoping, reviewer assignment, automated reminders and full decision tracking. All decisions are historized and directly usable during ISO 27001, SOC 2 or regulatory audits.
How can access legitimacy be demonstrated during an internal or regulatory audit?
Demonstrating access legitimacy requires answering four key questions: why access exists, who approved it, when, and according to which rules.
Ignimission centralizes governance rules, approval workflows and recertification decisions, providing a coherent and defensible audit trail.
What is ISPM (Identity Security Posture Management) in an IGA context?
ISPM focuses on continuously assessing identity security posture: excessive permissions, access drift and high-risk identities.
Within Ignimission, this approach is embedded into IGA governance through access analysis, anomaly detection and targeted recertifications or remediation workflows, while keeping decisions under human control.
How to manage the cumulative rights associated with internal mobility (Joiner/Mover/Leaver)?
Internal mobility is one of the main causes of excessive accumulation of rights and increased risk. Effective IGA governance relies on the ability to recalculate access rights when employees change roles and to automatically revoke rights that have become obsolete.
Ignimission uses existing HR and IAM repositories to trigger these recalculations, align rights with actual job roles, and submit new access requests for approval.
This approach permanently reduces access abuse while maintaining complete traceability of decisions.
What is the best identity management software in a GRC context?
There is no single “best” IGA solution for all organizations. The right choice depends on maturity level, scope and regulatory requirements.
In a GRC context, an IGA solution must govern access rights, trace decisions, run audit-ready recertifications and integrate with existing IAM tools. Ignimission is designed to address governance and compliance needs,
rather than replacing authentication or access enforcement components.